Scaling Security: Why the Swissbit iShield Key2 Needs Versasec vSEC:CMS

Passwordless Multi-Factor Authentication (MFA) is no longer a perk; it’s a foundational, non-negotiable layer of security against pervasive threats like phishing attacks and credential stuffing.
For large organizations demanding both uncompromised protection and massive scalability, the Swissbit iShield Key2 is a leading hardware authenticator available today that serves as a robust security anchor.

The Scaling Challenge: From Security Asset to IT Nightmare
Deploying at scale, however, even a multi-functional device like the iShield Key 2 can introduce significant operational challenges. Without central oversight, managing the lifecycle of thousands of hardware keys, from issuance and onboarding to PIN resets and revocation, can quickly turn security gains into an unmanageable IT nightmare.
How do you enforce consistent policies? How do you handle a lost key? How do you provision 5,000 keys without pulling your IT team off strategic projects for a month?
The Solution: Versasec as the Essential Operational Backbone
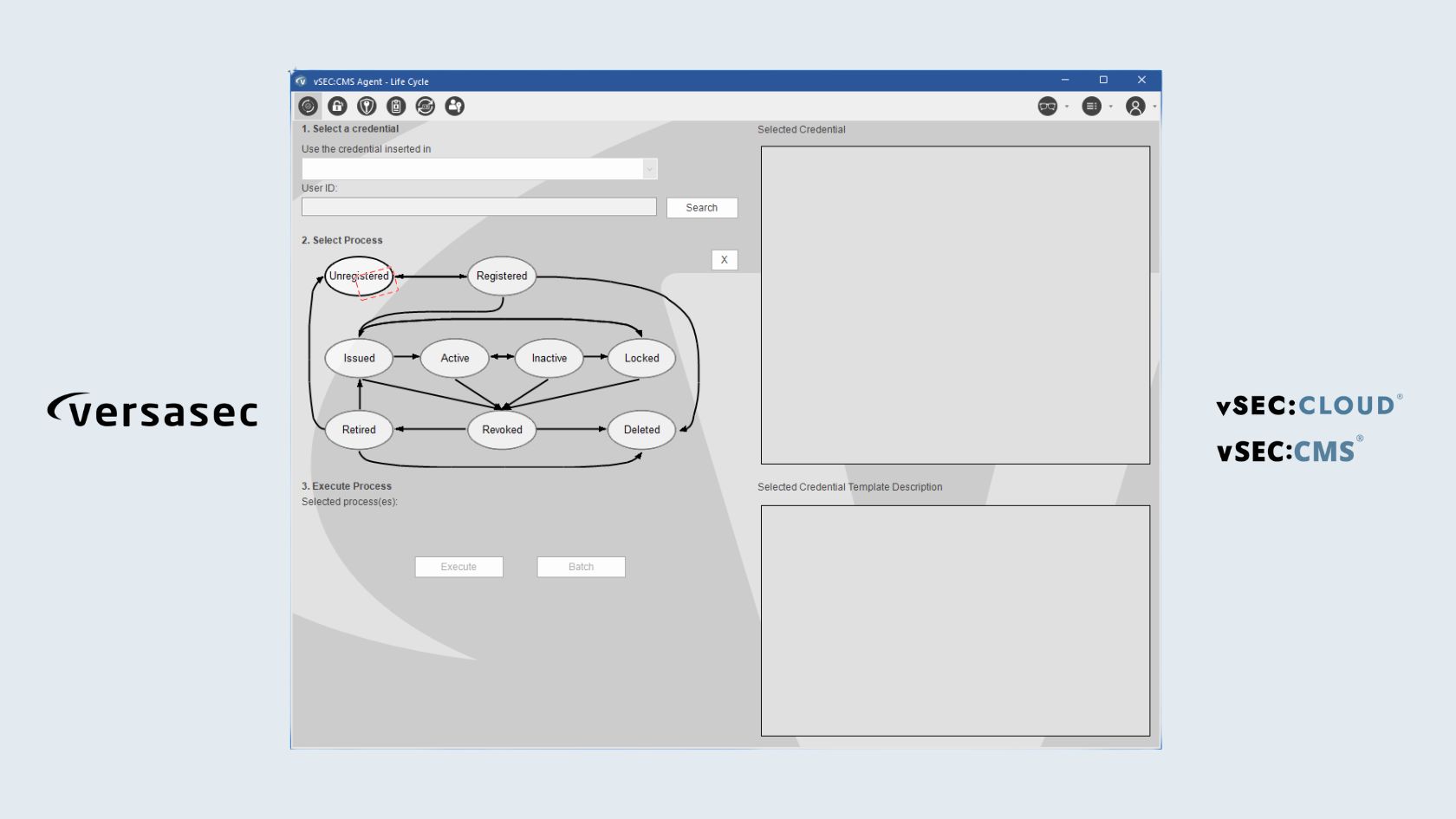
This is where Versasec’s vSEC:CMS (for on-premise) and vSEC:CLOUD (as a SaaS solution) become the essential operational backbone. These platforms transform complex security deployments into manageable, scalable, and compliant operations by delivering a centralized platform for the complete, end-to-end lifecycle management of the Swissbit iShield Key2.
How Versasec + Swissbit Deliver Scalable Security
This powerful partnership delivers tangible benefits that solve the core challenges of deploying hardware authentication on a scale.
1. Simplified Policy Enforcement and Compliance
Versasec brings security policy out of spreadsheets and into a unified, automated system.
- Centralized management ensures the consistent application of security policies across every issued key, regardless of its primary use (FIDO2 or PKI). This instantly eliminates risky shadow IT practices.
- Every single action on a key (issuance, revocation, PIN reset) is logged. This provides detailed, automated audit trails crucial for compliance with stringent regulations like NIS2, GDPR, U.S. EO14028, CISA, and NIST.
2. Streamlined Onboarding and Offboarding
Manual key provisioning for thousands of users is time-consuming and prone to error. Versasec automates this entire process.
- Massive, automated issuance: IT admins can automate the issuance of thousands of keys with pre-loaded certificates or FIDO2 credentials. vSEC:CMS connects seamlessly with existing directories (AD, Entra ID, or LDAP) and Certificate Authorities, making mass onboarding incredibly efficient.
- Instant, secure offboarding: If an employee leaves or a key is reported lost, vSEC:CMS allows for the immediate, simultaneous revocation of all associated credentials (PKI and FIDO2), minimizing the window of vulnerability to virtually zero.
3. Cost-Effectiveness and Reduced Helpdesk Load
Automation directly translates to lower operational costs (OpEx) and a smarter allocation of resources.
- User self-service: Users are empowered to manage common tasks like PIN unblock/reset and even request new keys through a self-service portal. This drastically reduces the number of time-consuming helpdesk tickets related to basic key management.
- Reduced human error: By automating security-critical processes, the platform reduces manual intervention, significantly lowering the potential for costly human error.
- Maximized ROI: Automating key lifecycle management frees up valuable IT resources to focus on strategic security initiatives, maximizing the return on your hardware investment.
A Unified, Automated Solution
The powerful partnership between the Swissbit iShield Key2 hardware and Versasec’s vSEC:CMS and vSEC:CLOUD management platforms delivers a unified, automated, and highly compliant solution. Together, they transform complex hardware security from a potential operational burden into a highly efficient and scalable part of your enterprise operations.
Our experts are happy to help.
Receive the latest news and announcements about storage and security solutions as well as current events and new products.